7 Shocking Reasons Google Dark Web Report Ends in 2026
Google Dark Web Report, once a key shield against data leaks, faces full shutdown in 2026. This tool scanned hidden
Personal Cybersecurity: Tips and tools to protect data, secure devices, and defend against online threats.

Google Dark Web Report, once a key shield against data leaks, faces full shutdown in 2026. This tool scanned hidden

WhatsApp ghost pairing scam is the latest attack method criminals are using to quietly mirror your chats, photos and documents without
AI third-party risk is becoming the new frontier in cybersecurity. As developers rush to adopt AI-assisted coding tools and open-source

Introduction Picture this: You’re at a high-security party where every guest—even regulars—gets scanned at every door, no matter how many
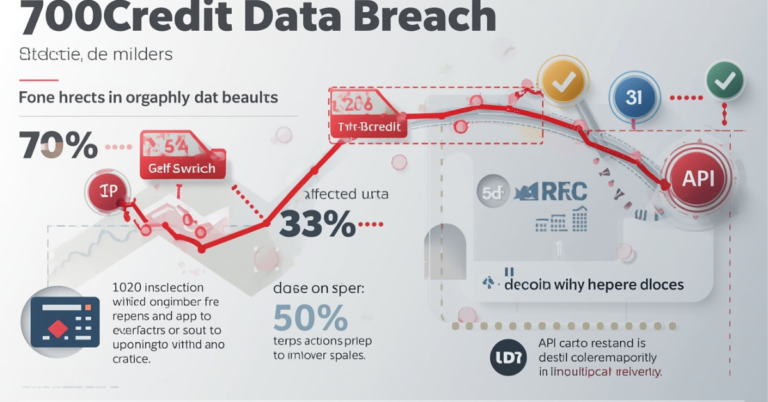
The 700Credit data breach has rocked North America’s automotive sector, exposing sensitive data of 5.8 million individuals. Hackers targeted a
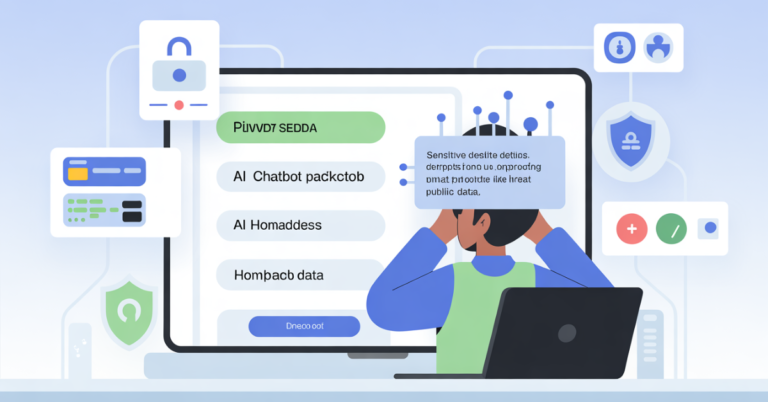
AI chatbot privacy risks are no longer theoretical—they are baked into how modern models learn from your data. As AI
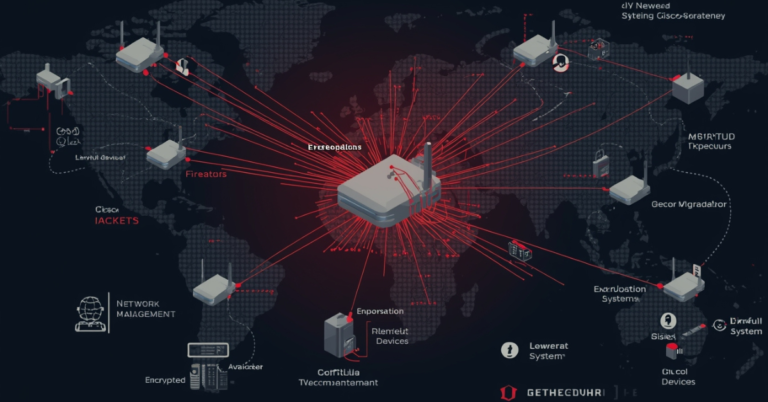
Cisco-trained hackers are now at the forefront of one of the most sophisticated global espionage campaigns targeting Cisco devices themselves.

Introduction If your entire digital life lives on your phone, learning how to secure your Android is no longer optional.

Chrome $20K AI Security Bounty grabs headlines as Google challenges hackers to crack its new agentic defenses. This program offers

Phone scam prevention has become a critical digital skill in 2025 as cybercriminals transform scam calls into sophisticated social-engineering campaigns. These