
How to Secure Your Android in 10 Easy Steps (2025 Guide)
Introduction If your entire digital life lives on your phone, learning how to secure your Android is no longer optional.

Introduction If your entire digital life lives on your phone, learning how to secure your Android is no longer optional.

Chrome $20K AI Security Bounty grabs headlines as Google challenges hackers to crack its new agentic defenses. This program offers
Small European businesses AI adoption surges, enabling micro-firms to compete with giants through tools once reserved for big budgets. LinkedIn

The Huntsville ransomware attack rocked this Ontario town in March 2024, exposing sensitive personal information after hackers infiltrated municipal networks.

AI tools for productivity 2025 are transforming chaotic workflows into streamlined powerhouses, letting professionals like web developers and SaaS builders focus
Phone scam prevention has become a critical digital skill in 2025 as cybercriminals transform scam calls into sophisticated social-engineering campaigns. These

Mike Boddicker Davenport IT Director appointment marks a pivotal shift for Davenport’s technology landscape. Bringing proven expertise from Army Contracting
The Virtual Cell Challenge at NeurIPS 2025 has redefined how artificial intelligence and biology intersect. This first-of-its-kind global competition rewarded models that

BigBear.ai Middle East expansion signals a pivotal moment in the global AI landscape. The U.S.-based mission-ready AI leader has opened its
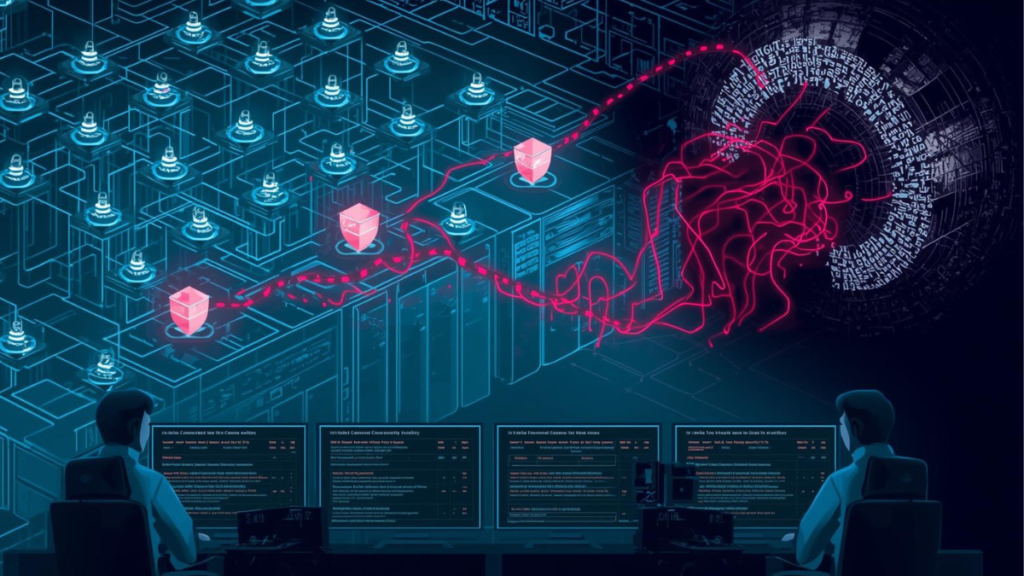
China-linked Brickstorm malware is the latest wake-up call for any organization running critical workloads on VMware. US and Canadian cybersecurity